Cloudflare DDoS Protection
When running an ARK node, especially a Delegate Node, you should consider your server’s security as your main priority.
Warning
During this guide, we will configure network and SSH parameters, which if improperly performed might permanently lock you out of your server. Ensure you fully understand each step before proceeding.
DDOS Protection With Cloudflare
In this section, we’re going to setup Cloudflare and SSL for DDoS protection and security using Nginx as a reverse proxy.
Install Nginx
1sudo apt-get install nginxEdit Nginx Config
1sudo nano /etc/nginx/sites-enabled/defaultPaste in the following config, making sure you edit the server_name and proxy_pass. You may need to change ssl_certificate and ssl_certificate_key if you name your files something different.
File: /etc/nginx/enabled-sites/default
1# HTTPS 2server { 3 listen 443 ssl; 4 server_name node.yoursite.com; 5 ssl_certificate /etc/nginx/ssl/ark.crt; 6 ssl_certificate_key /etc/nginx/ssl/ark.key; 7 ssl_verify_client off; 8 ssl_protocols TLSv1 TLSv1.1 TLSv1.2; 9 ssl_ciphers EECDH+CHACHA20:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5;10 ssl_prefer_server_ciphers on;11 location / {12 proxy_set_header X-Real-IP $remote_addr;13 proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;14 proxy_set_header X-NginX-Proxy true;15 proxy_pass http://localhost:4001/;16 proxy_ssl_session_reuse off;17 proxy_set_header Host $http_host;18 proxy_cache_bypass $http_upgrade;19 proxy_redirect off;20 }21}Press CTRL+X to exit the file, Y to save the file, and ENTER to write to the file and return to the command line.
Cloudflare / SSL Setup
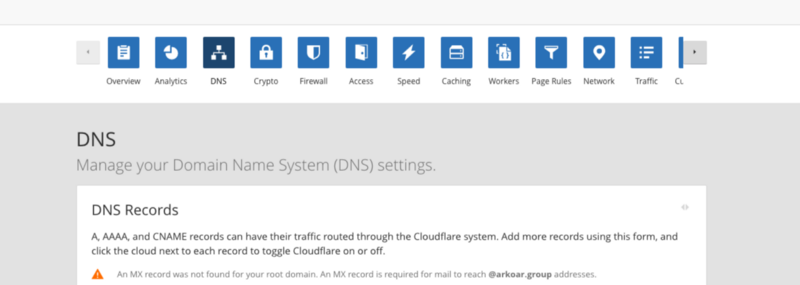
Login to your Cloudflare dashboard and click on the DNS button.
Then go to Crypto.
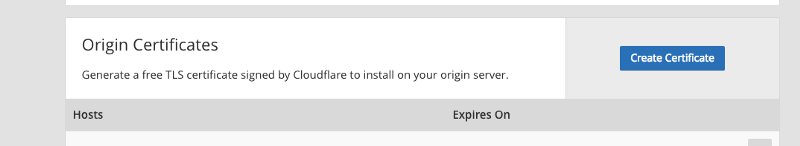
Scroll down to Origin Certificates and click the Create Certificate button. Keep this window open after Cloudflare generates your two keys.
Open Terminal on your ARK node server
We need to create a new folder and copy our keys to our server.
1mkdir /etc/nginx/ssl2cd /etc/nginx/ssl3touch ark.crt ark.keyCopy the PRIVATE KEY to the file ark.key and the CERTIFICATE to ark.crt.
Start Nginx
1sudo service nginx startIf everything started fine, you should be able to access your ARK node APIs behind SSL. Giving you the bonus of Cloudflare DDOS protection.
Otherwise, if you get any errors run the following command to troubleshoot nginx.
1sudo nginx -t -c /etc/nginx/nginx.confConclusion
Your node is now very secure. With this setup, you can open and close your SSH port remotely using a secret knocking technique as well as sign in using cryptographic keys.